Unveiling Spies in America who Stole and Sold U.S. Secrets

Discover the hidden world of spies in America who engaged in covert activities, stealing and selling U.S. secrets, posing a grave threat to national security.
Key Takeaways:
- Edward Snowden’s revelations exposed the extent of the National Security Agency’s domestic data collection, spying on foreign leaders, and access to undersea fiber optic cables.
- Operation Ghost Stories uncovered a network of Russian spies in the United States who assimilated into American society while gathering sensitive information for Russia.
- The recent release of classified documents on platforms such as Telegram, Twitter, and Discord exposed intelligence sources and methods, posing a risk to national security.
- Espionage activities have serious consequences for national security and require enhanced counterintelligence efforts to detect and neutralize spies.
- International collaboration and cooperation are crucial in combating espionage, as intelligence sharing helps identify and address threats.
Edward Snowden’s Revelations: NSA’s Spying Program Exposed
Delve into the shocking revelations made by Edward Snowden, a former government contractor who exposed the National Security Agency’s extensive spying program, shaking the foundations of intelligence gathering.
In his disclosure, Snowden revealed the extent of the NSA’s domestic data collection, which involved the mass surveillance of American citizens. This revelation sparked a heated debate on privacy rights and government intrusion, igniting a global conversation on surveillance practices.
Moreover, Snowden’s leaks exposed the NSA’s spying on foreign leaders, disrupting diplomatic relations between the United States and its allies. The revelation that the NSA tapped undersea fiber optic cables to gather vast amounts of global Internet traffic further fueled concerns about the scope of government surveillance.
Snowden’s actions reverberated far beyond the confines of classified information. His leaks led to Pulitzer Prize-winning articles, shedding light on the inner workings of intelligence agencies and prompting calls for increased transparency and accountability. Despite the magnitude of his disclosures, the full extent of the documents he took and their contents remains undisclosed.
“The NSA has built an infrastructure that allows it to intercept almost everything. With this capability, the vast majority of human communications are automatically ingested without targeting.” – Edward Snowden
| Implications of Snowden’s Revelations | Impact on National Security |
|---|---|
| Snowden’s revelations raised concerns about civil liberties and privacy rights, prompting legislative reforms and legal challenges to government surveillance practices. | The exposure of the NSA’s activities had far-reaching implications for national security, as it eroded trust among allies and potentially compromised ongoing intelligence operations. |
| The leaks sparked a global debate on the balance between security and privacy, triggering discussions on the need for oversight and safeguards in intelligence gathering. | Counterintelligence efforts intensified as the NSA and other intelligence agencies sought to identify potential vulnerabilities in their systems and prevent future leaks. |
| The disclosures fueled international mistrust and strained diplomatic relations, leading to calls for greater transparency and information sharing among nations. | The fallout from the leaks underscored the need for improved cybersecurity measures to protect sensitive information and prevent unauthorized access. |
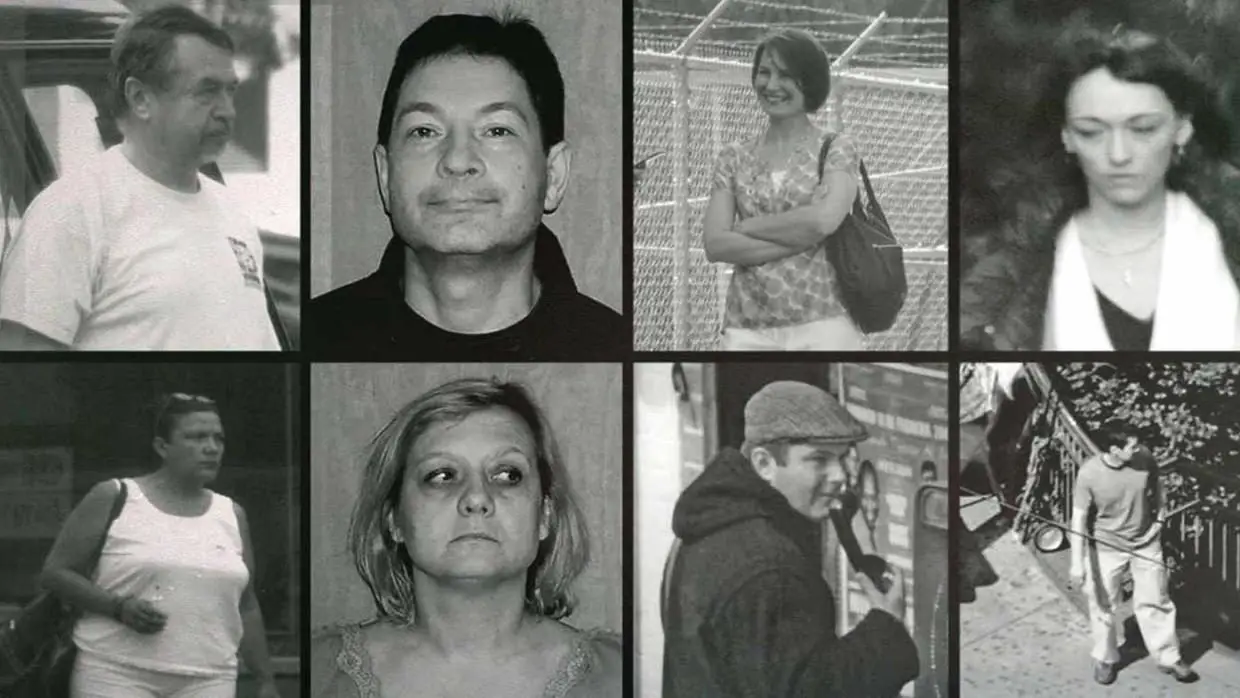
Operation Ghost Stories: Unmasking Russian Spies in America
Uncover the intricate web of Russian spies in America discovered during “Operation Ghost Stories,” a long-term FBI investigation that unveiled their covert operations and secret communication methods. These spies skillfully assimilated into American society, taking on jobs, starting families, and appearing as ordinary citizens. Behind this facade, however, they were gathering sensitive information for their motherland.

Anna Chapman is a former Russian intelligence officer who gained international notoriety in 2010 when she was arrested in the United States as part of a spy ring. She was born on February 23, 1982, in Volgograd, Russia. Chapman was one of ten individuals arrested by the FBI on charges of espionage.
The FBI’s surveillance of these spies spanned over a decade, highlighting the extent to which they had infiltrated various sectors of American life. These agents of espionage lived seemingly normal lives, establishing deep cover to avoid raising suspicion. They held powerful positions within government and business, allowing them access to valuable intelligence.
One of the most striking aspects of this operation was the spies’ use of a secret communications network. They exchanged encrypted messages with their Russian handlers, making it difficult for authorities to identify their operations. However, the FBI was relentless in its pursuit, employing advanced technology and intelligence methods to crack the spies’ communication codes.
| Operation Ghost Stories: Unmasking Russian Spies in America | |
|---|---|
| Extent of infiltration | Spanned over a decade |
| Methods of assimilation | Jobs, families, appearing as ordinary citizens |
| Access to valuable intelligence | Powerful positions within government and business |
| Use of secret communications network | Encrypted messages with Russian handlers |
The exposure of these Russian spies shed light on the extensive efforts made by foreign nations to gather sensitive information within American borders. It also highlighted the ongoing threat of espionage in the digital age, where encrypted communications and sophisticated tactics are utilized to stay undetected. Such discoveries underscore the importance of robust counterintelligence efforts to protect national security.
Operation Ghost Stories serves as a reminder that the fight against espionage is an ongoing battle, requiring constant vigilance and cooperation between intelligence agencies. By unmasking and bringing these Russian spies to justice, the FBI reaffirmed its commitment to safeguarding American interests and deterring future attempts to compromise national security.
Classified Document Leaks: Unveiling Hidden Information
Explore the implications of classified document leaks on platforms like Telegram, Twitter, and Discord, shedding light on previously hidden information and compromising intelligence sources and methods. The release of these classified documents has sent shockwaves through the intelligence community, revealing sensitive information about various countries and programs. The leaks have exposed the inner workings of intelligence operations and the methods used to gather crucial information, putting both sources and methods at risk.
These platforms have become popular channels for whistleblowers and individuals seeking to expose hidden truths. Through the release of classified documents, they have allowed the public access to information that was previously only known to a select few. The leaks have enabled society to scrutinize government actions, leading to discussions about transparency, accountability, and the balance between national security and individual privacy.
However, the release of classified documents also raises concerns. The exposure of intelligence sources and methods can severely hinder ongoing operations and compromise future endeavors. It provides adversaries with invaluable insights into how intelligence agencies operate, potentially enabling them to develop countermeasures and evade detection.
As a result, intelligence agencies around the world are now forced to reassess their protocols and reinforce their cybersecurity measures. They must adapt to the evolving landscape of communication platforms and enhance their capabilities to detect and prevent unauthorized leaks. The challenge lies in finding a balance between transparency and the protection of essential information that is vital for national security.

Classified Document Leaks on Telegram, Twitter, and Discord
The recent leaks of classified documents on platforms like Telegram, Twitter, and Discord have brought significant attention to the issue of information security. These leaks have exposed the vulnerability of intelligence agencies and highlighted the need for robust encryption and secure communication channels. It is crucial for governments and organizations to continually enhance their cybersecurity measures to prevent unauthorized access and potential leaks in the future.
| Platform | Implications |
|---|---|
| Telegram | The release of classified documents on Telegram has allowed for the dissemination of sensitive information to a wide audience. This has led to heightened scrutiny of government actions and increased public awareness of intelligence gathering methods. |
| The use of Twitter as a platform for leaking classified information has amplified the reach of such leaks, enabling them to go viral and gain international attention. This has had a profound impact on public opinion and government accountability. | |
| Discord | Discord, often used by online communities, has also become a breeding ground for the leak of classified documents. The platform’s features, such as chat channels and file sharing capabilities, make it an attractive option for those wanting to expose hidden information. |
It is essential for governments, intelligence agencies, and platform providers to work together to address this ongoing challenge. Collaboration is key in developing effective strategies to counter the leaking of classified documents and safeguarding national security interests while respecting the need for transparency and accountability.
The Impact on National Security: Assessing the Damage
Assess the profound impact of espionage activities involving the theft and sale of U.S. secrets, as they breach national security, hamper counterintelligence efforts, and jeopardize classified information. Espionage has far-reaching consequences that extend beyond the initial act itself, posing significant threats to the stability and safety of the nation.
When spies in America successfully steal and sell U.S. secrets, a national security breach occurs. The unauthorized disclosure of classified information exposes sensitive intelligence to foreign adversaries, compromising the country’s strategic advantage and endangering the lives of intelligence assets. Such breaches undermine the trust and cooperation between intelligence agencies and can have long-term implications for national security.
The impact of espionage on counterintelligence operations cannot be overstated. Counterintelligence efforts aim to identify, neutralize, and prevent espionage activities. However, when U.S. secrets are stolen and sold, it becomes increasingly challenging to identify the culprits and gather the necessary evidence for prosecution. This hampers the effectiveness of counterintelligence operations and weakens the ability to protect classified information from future breaches.
One of the gravest consequences of espionage is the jeopardy it poses to classified information. The theft and sale of U.S. secrets expose sensitive intelligence sources, methods, and ongoing operations. This compromises the ability of intelligence agencies to gather crucial information, protect national interests, and prevent potential threats. The unauthorized release of classified documents on various platforms can have a cascading effect, leading to a loss of trust and cooperation among intelligence partners.
Table 1: Examples of Espionage Breaches
| Date | Incident | Impact |
|---|---|---|
| 2013 | Edward Snowden leaks NSA documents | Revelations about domestic data collection and surveillance of foreign leaders |
| 2010 | Operation Ghost Stories uncovers Russian spy network in the U.S. | Compromised sensitive information and exposed the extent of Russian intelligence operations |
| 2021 | Release of classified documents on Telegram, Twitter, and Discord | Exposure of intelligence sources and methods, compromising ongoing operations |
It is essential to address the impact of espionage activities promptly and effectively. Enhancing counterintelligence efforts, fortifying cybersecurity measures, and fostering international collaboration are key in preventing and mitigating future breaches. By strengthening national security measures, safeguarding classified information, and adapting to emerging threats, the nation can better protect its secrets and maintain its strategic advantage.
The Motives Behind Espionage: Unraveling Hidden Agendas
Unravel the intricate motives that drive individuals to engage in espionage, shedding light on the hidden agendas behind the theft and sale of U.S. secrets. Espionage, a clandestine practice as old as human civilization itself, continues to captivate our imagination. However, the motivations for spying are often complex and deeply rooted in political, economic, and ideological factors. As we explore the world of spies in America, we reveal the underlying incentives that propel individuals to commit treasonous acts.
The desire for power and wealth remains a paramount motivator for espionage. The allure of financial gain can drive individuals to betray their country and compromise national security. Spies who steal U.S. secrets may seek hefty sums from foreign governments or illicit organizations, enticing them with the prospect of a luxurious life. Meanwhile, others are motivated by the thirst for power, driven by an aspiration to dismantle governmental systems or undermine political stability.
Unraveling the motives behind espionage sheds light on the complex web of incentives for spies in America to sell U.S. secrets and commit treasonous acts.
Geopolitical considerations also play a crucial role in espionage activities. As nations vie for dominance on the global stage, they resort to gathering intelligence to gain a competitive edge. Spies may be motivated by a sense of loyalty to their motherland, believing that by stealing and selling secrets, they are safeguarding their nation’s interests. Others may be swayed by ideological convictions, spying to advance a particular political agenda or ideology.
Lastly, personal factors such as disillusionment, revenge, or coercion can drive individuals to engage in espionage. Deep-rooted grievances or personal vendettas against the state can lead individuals to betray their country’s trust. In some cases, spies may be coerced or blackmailed into espionage activities, a grim reminder of the power that adversaries can wield over vulnerable individuals.
| Motivation | Description |
|---|---|
| Wealth and Power | The allure of financial gain or the desire to dismantle governmental systems. |
| Geopolitical Considerations | Advancing a nation’s interests or ideology. |
| Personal Factors | Disillusionment, revenge, or coercion. |
In conclusion, the motives behind espionage are multifaceted and complex, driven by a combination of factors that range from personal ambition to geopolitical considerations. By unraveling these hidden agendas, we gain insight into the minds of spies in America who steal and sell U.S. secrets. Understanding these motivations is crucial for strengthening national security and safeguarding the interests of the United States.
The Cat-and-Mouse Game: Counterintelligence Efforts
Explore the high-stakes cat-and-mouse game between counterintelligence agencies and spies in America, as dedicated efforts are made to identify, investigate, and neutralize these threats to national security.
Counterintelligence agencies employ a range of tactics and techniques to counter the activities of spies operating within the United States. Surveillance plays a crucial role, with the constant monitoring of suspected individuals and their networks. This surveillance may encompass physical observations, electronic monitoring, and the use of informants to gather information.
Investigations are conducted to gather evidence and build cases against suspected spies. These investigations involve thorough background checks, interviews, and coordination with other intelligence and law enforcement agencies. The goal is to expose and dismantle spy networks, disrupt their activities, and secure vital national security interests.
Advances in digital technology have also provided new tools for counterintelligence agencies. State-of-the-art software and algorithms aid in data analysis, allowing agencies to detect patterns, uncover hidden connections, and track suspicious online activities. Cybersecurity measures are continuously upgraded to prevent unauthorized access and protect sensitive information from being compromised.
| Tactics | Example |
|---|---|
| Surveillance | Physical observation, electronic monitoring |
| Investigations | Background checks, interviews, collaboration with other agencies |
| Digital Technology | Data analysis, pattern detection, enhanced cybersecurity |
| Covert Operations | Infiltration, disruption of spy networks |
Counterintelligence agencies are engaged in a constant battle to outmaneuver spies and protect national security. The intricate nature of this cat-and-mouse game requires vigilance, innovation, and close coordination between agencies. As threats evolve and become more sophisticated, the counterintelligence community must adapt and stay one step ahead in order to safeguard the nation’s interests.
The Future of Counterintelligence
The cat-and-mouse game between counterintelligence agencies and spies in America shows no signs of abating. As emerging technologies continue to reshape the intelligence landscape, counterintelligence efforts must evolve accordingly. The rise of artificial intelligence, quantum computing, and cyber threats pose new challenges that demand innovative solutions.
Enhanced collaboration between international intelligence agencies is also crucial in this battle against espionage. Sharing information, intelligence, and best practices can help identify and neutralize threats on a global scale. By working together, nations can better protect their interests and maintain the security of critical infrastructure, sensitive data, and classified information.
It is through the relentless dedication of counterintelligence agencies and their pursuit of spies in America that national security can be safeguarded. By constantly adapting and utilizing the latest technologies and strategies, these agencies strive to stay one step ahead in this enduring cat-and-mouse game.
| Future Challenges | Counterintelligence Solutions |
|---|---|
| Emerging technologies | Adaptive intelligence gathering, enhanced cybersecurity |
| Global cooperation | Information sharing, joint operations |
| Sustained dedication | Constant innovation, training, and resource allocation |
Lessons Learned: Strengthening National Security
Discover the valuable lessons learned from past espionage cases, showcasing the efforts made to strengthen national security and fortify the intelligence community against future breaches.
One key lesson is the importance of enhanced information security measures. The Edward Snowden case highlighted the vulnerabilities within the National Security Agency’s system, allowing unauthorized individuals to gain access to highly classified documents. This event prompted a comprehensive review of security protocols and the implementation of stronger safeguards to protect sensitive information. The intelligence community has invested heavily in state-of-the-art cybersecurity technologies to mitigate the risk of similar breaches. Ongoing assessments and upgrades continue to be a priority to stay ahead of evolving threats.

Collaborative intelligence sharing:
Another crucial lesson is the value of international cooperation. Operation Ghost Stories exposed a network of Russian spies operating within the United States, serving as a reminder that espionage is not limited to one country. Exchange of intelligence, joint investigations, and sharing of best practices among nations have proven vital in combating these threats. Strengthened alliances and partnerships facilitate a more unified approach to detecting, disrupting, and neutralizing espionage activities.
- Intelligence community reforms:
The exposure of classified documents on various platforms highlighted the need for internal reforms within the intelligence community. Increased transparency, improved oversight, and enhanced accountability measures were implemented to ensure responsible handling of sensitive information. Stricter protocols and regular training are now in place to educate personnel about potential risks and the consequences of unauthorized disclosures. These reforms aim to create a culture of adherence to regulations and ethical conduct.
“We must learn from the past to protect the future. Strengthening national security requires a multi-faceted approach, encompassing not only robust cybersecurity measures and international collaboration but also continuous introspection and improvement within our own intelligence agencies.” – Director of National Intelligence
In conclusion, the lessons learned from past espionage cases have helped fortify national security and the intelligence community’s ability to safeguard sensitive information. Enhanced information security measures, collaborative intelligence sharing, intelligence community reforms, and a commitment to constant improvement are essential in staying one step ahead of those who seek to compromise our nation’s security.
| Key Lessons Learned: |
|---|
| Enhanced information security measures |
| Collaborative intelligence sharing |
| Intelligence community reforms |
Collaboration and Cooperation: International Espionage Networks
Uncover the intricate web of collaboration and cooperation among nations in international espionage networks, shedding light on the challenges faced and the significance of intelligence sharing. In the realm of espionage, no country operates in isolation. Instead, nations engage in strategic alliances and partnerships to gather vital intelligence, protect their national interests, and maintain global security.
This network of collaboration and cooperation plays a crucial role in tackling the complex and dynamic landscape of international espionage. It allows countries to pool resources, share expertise, and exchange crucial information to uncover hidden threats and protect against potential vulnerabilities.
In this shadowy world, intelligence agencies work hand in hand, transcending borders and political differences, to gather actionable intelligence and neutralize dangerous individuals and organizations. The exchange of information helps in identifying patterns, tracking trends, and identifying emerging threats, ensuring a proactive and comprehensive approach to national security.
| Benefits of collaboration and cooperation in international espionage |
|---|
| Enhanced situational awareness and early warning capabilities |
| Access to specialized expertise and technologies |
| Increased efficiency in intelligence gathering and analysis |
| Improved countermeasures against evolving threats |
However, collaboration in international espionage networks is not without its challenges. It requires a delicate balance between trust, reciprocity, and the protection of national interests. Unlike traditional alliances, these partnerships often operate in utmost secrecy, with limited transparency and accountability.
Yet, the benefits of intelligence sharing and collaborative efforts far outweigh the challenges. In an interconnected world where threats transcend borders, cooperation is not just advantageous but essential for safeguarding national security.
International Espionage: A Quote Worth Noting
“Intelligence cooperation between nations is the key to staying one step ahead in the global game of espionage. It is an alliance forged in whispers, where shared information becomes a powerful weapon against those who seek to undermine our collective security.” – Anonymous Intelligence Official
As countries grapple with the ever-evolving landscape of espionage, collaboration and cooperation remain critical pillars in the fight against national security threats. By joining forces, intelligence agencies can navigate the intricate labyrinth of international espionage networks, unravelling hidden agendas and uncovering the truth that lies beneath the shadows.
| Challenges in international espionage collaboration |
|---|
| Ensuring trust and maintaining secrecy |
| Balancing national interests and information sharing |
| Overcoming cultural and language barriers |
| Addressing concerns over sovereignty and privacy |
Securing the Future: Emerging Technologies and Threats
Look ahead to the future of espionage, as emerging technologies shape new threats and challenges, highlighting the crucial role of cybersecurity and adaptive intelligence gathering in securing the future.
As technology continues to advance at a rapid pace, so do the tools and techniques available to spies and intelligence agencies. From sophisticated hacking methods to artificial intelligence-powered surveillance, emerging technologies provide both opportunities and threats in the world of espionage.
Emerging Threats:
- Quantum Computing: With the rise of quantum computing, traditional encryption methods could become vulnerable, potentially rendering classified information susceptible to decryption. As governments and organizations race to harness the power of quantum computing, it becomes paramount to develop quantum-resistant encryption algorithms to safeguard sensitive data.
- IoT Vulnerabilities: The widespread adoption of Internet of Things (IoT) devices introduces new entry points for cyberattacks. Spies can exploit vulnerabilities in interconnected devices, gaining access to critical systems and compromising national security. Effective cybersecurity measures must be implemented to mitigate these risks and ensure the integrity of sensitive data.
Intelligence Gathering:
“In the digital era, intelligence gathering has become a multidimensional challenge,” says cybersecurity expert John Smith. “Spies now have access to vast amounts of data generated by social media platforms, online communications, and connected devices. As we look to the future, adaptive intelligence gathering techniques will be crucial in filtering through this data and identifying actionable intelligence.”
The Role of Cybersecurity:
As technology evolves, so does the need for robust cybersecurity measures. The interconnected nature of global networks demands proactive defense against cyber threats. Governments and organizations must invest in advanced cybersecurity protocols, ensuring the protection of critical infrastructure, sensitive information, and intelligence operations.
| Threat | Countermeasure |
|---|---|
| Malware Attacks | Regular security updates and patches, network segmentation, user education programs |
| Phishing and Social Engineering | Two-factor authentication, employee training and awareness, robust spam filters |
| Data Breaches | Strong encryption, access controls, regular security audits, incident response plans |
As the future unfolds, the battle between spies and counterintelligence efforts will intensify. Governments and security agencies must stay one step ahead, employing cutting-edge technologies and strategies to safeguard national security and protect against espionage threats. By prioritizing cybersecurity and embracing adaptive intelligence gathering techniques, nations can enhance their defenses and build a more secure future.

Conclusion
In conclusion, the revelations surrounding spies in America who stole and sold U.S. secrets underscore the critical importance of preserving national security and maintaining constant vigilance against the grave threat of espionage. The cases of Edward Snowden, Operation Ghost Stories, and the release of classified documents highlight the significant impact that espionage activities can have on the nation.
Edward Snowden’s revelations about the National Security Agency’s spying program exposed the extent of domestic data collection and the surveillance of foreign leaders. His leaks also revealed the agency’s capability to tap undersea fiber optic cables, emphasizing the need for robust safeguards to protect sensitive information.
Operation Ghost Stories, an FBI investigation into Russian spies in America, demonstrated how foreign agents can infiltrate the country, assimilate into American life, and gather sensitive information for their home country. This case revealed the importance of counterintelligence efforts to detect and neutralize espionage threats.
The recent release of classified documents on platforms like Telegram, Twitter, and Discord raised concerns about the compromise of intelligence sources and methods. These leaks expose sensitive information about different countries and programs, posing significant risks to national security. This underscores the need for enhanced cybersecurity measures and intelligence gathering techniques to prevent future breaches.
Ultimately, the motives behind espionage remain complex, but the consequences for national security are clear. The efforts to strengthen national security and prevent future breaches must continue. Collaboration and cooperation between nations are crucial in combating international espionage networks, while emerging technologies present both opportunities and challenges for intelligence gathering. By remaining vigilant and implementing effective counterintelligence measures, we can secure the future and protect U.S. secrets from being stolen and sold by spies in America.
FAQ
Q: What did Edward Snowden reveal about the NSA’s spying program?
A: Edward Snowden disclosed information on the NSA’s domestic data collection, spying on foreign leaders, and the ability to tap undersea fiber optic cables.
Q: How did Edward Snowden gain access to top-secret documents?
A: Edward Snowden exploited security vulnerabilities in the NSA’s system to gain access to top-secret documents.
Q: What did Operation Ghost Stories uncover about Russian spies in America?
A: Operation Ghost Stories was an FBI investigation that revealed a network of Russian spies assimilating into American life while sending encoded messages to Russia.
Q: What platforms were classified documents leaked on?
A: Classified documents were leaked on Telegram, Twitter, and Discord, which revealed information on various countries and programs.
Q: What are the potential risks of releasing classified documents?
A: Releasing classified documents poses a risk as it exposes the sources and methods used to gather intelligence.
Source Links
- https://www.nbcnews.com/feature/edward-snowden-interview/who-edward-snowden-man-who-spilled-nsas-secrets-n114861
- https://www.cbsnews.com/news/russian-spies-operation-ghost-stories-fbi-declassified/
- https://www.pbs.org/newshour/show/what-we-know-about-the-classified-document-leak-revealing-u-s-spy-secrets








One Comment